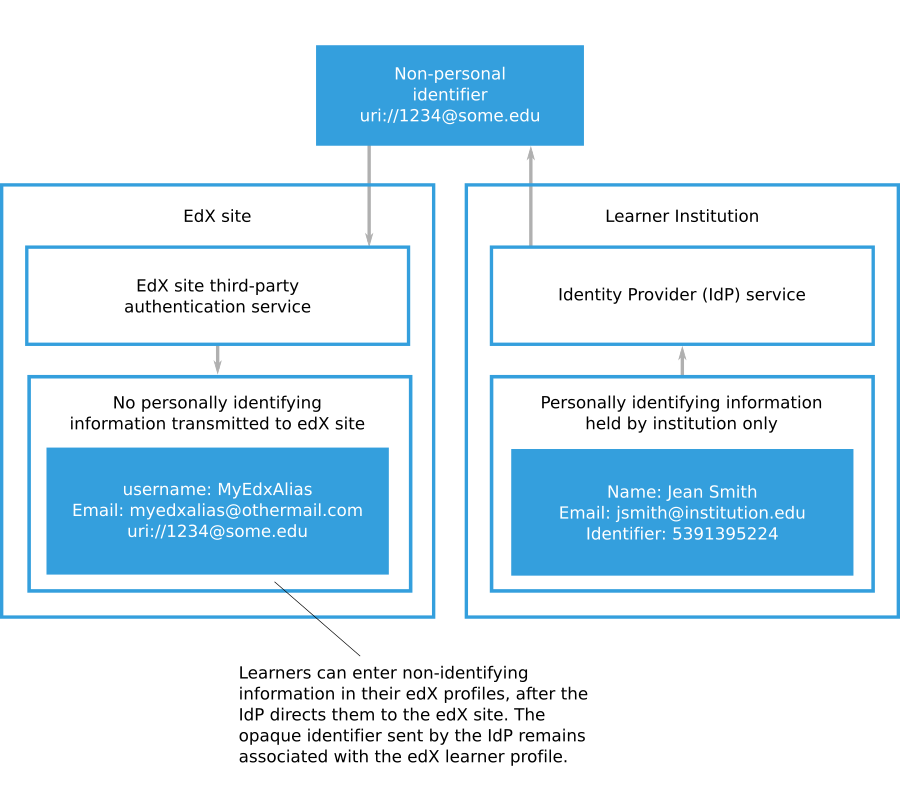
4.23.6. Eliminating PII From Third-Party Authentication — Installing, Configuring, and Running the Open edX Platform documentation

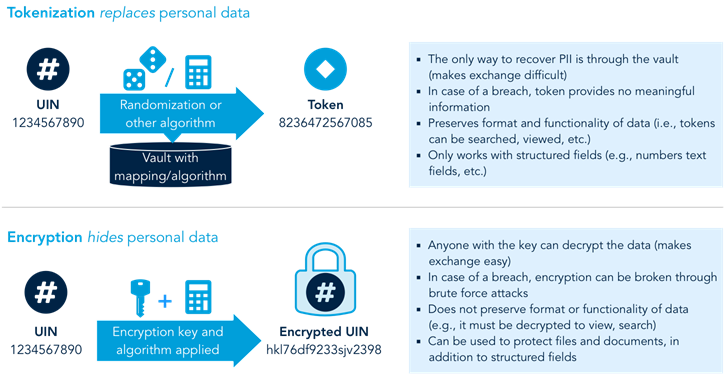
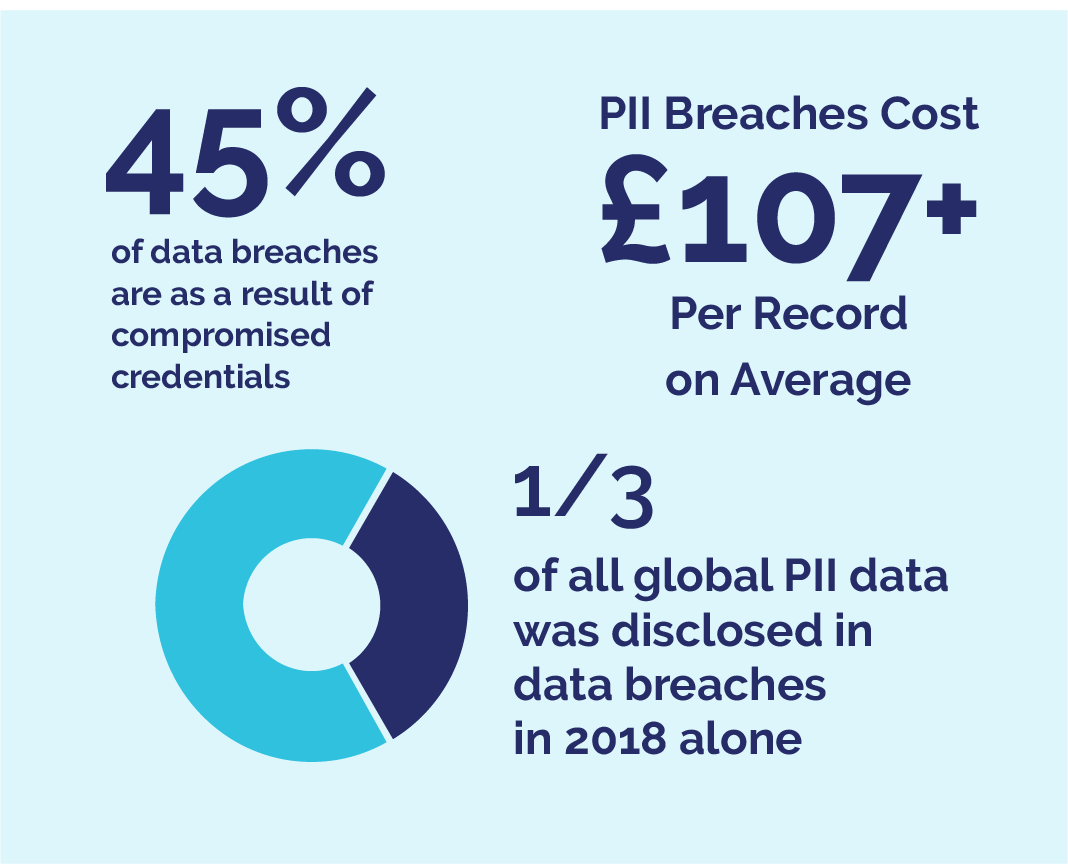
Why Should You Tokenize Sensitive Data Like PII, Credit Card? - Strac - Detect & Mask Sensitive Personal Data

De-identification and re-identification of PII in large-scale datasets using Cloud DLP | Cloud Architecture Center | Google Cloud

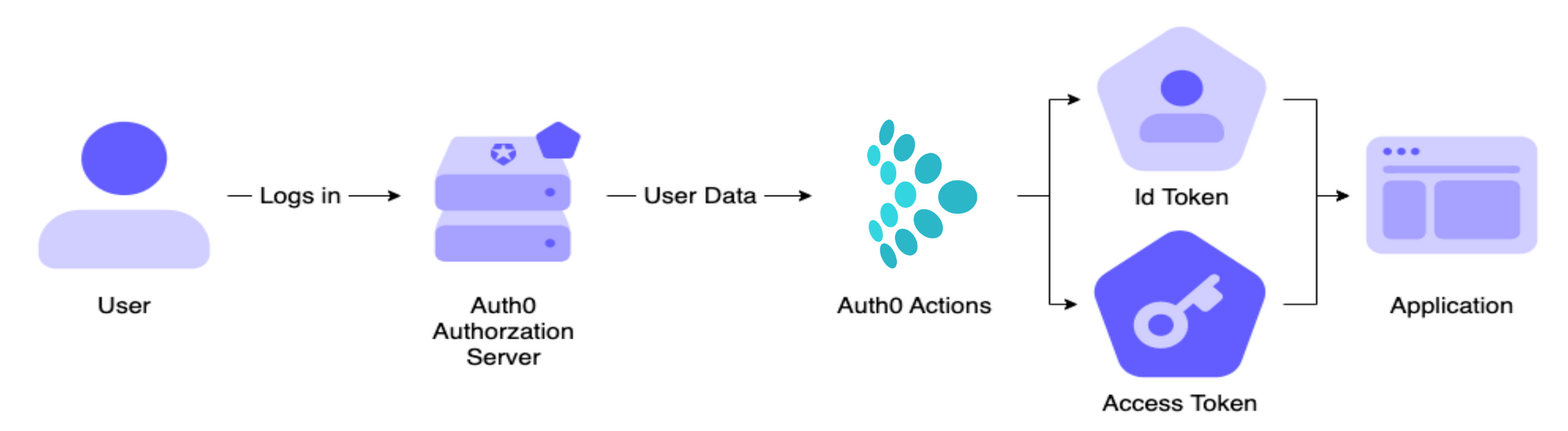
Debug Logging Microsoft.Identity.Client and the MSAL OAuth client credentials flow | Software Engineering
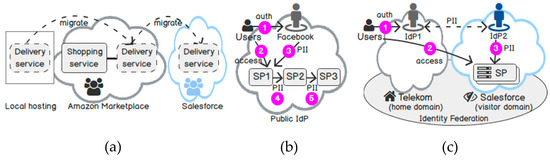
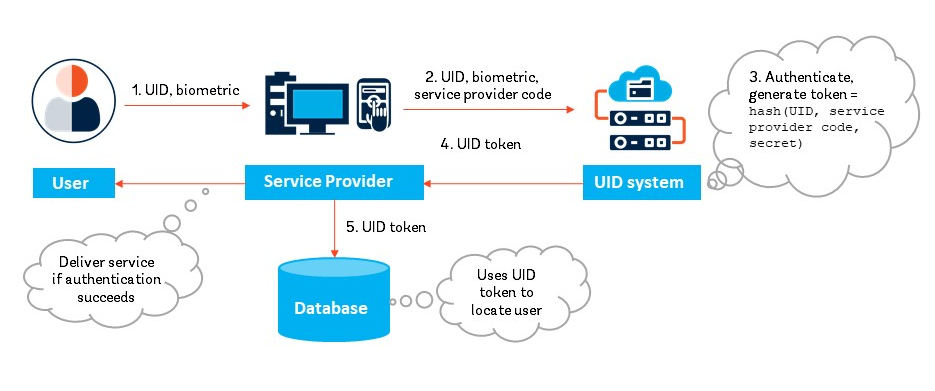
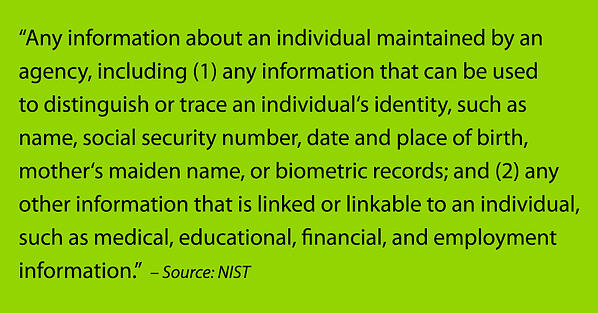
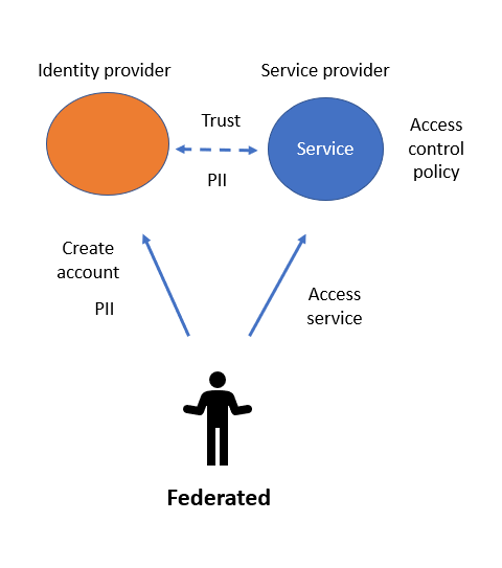
Future Internet | Free Full-Text | Identity-as-a-Service: An Adaptive Security Infrastructure and Privacy-Preserving User Identity for the Cloud Environment

.jpeg)